Globally trusted leader in cybersecurity education.
Step into the frontlines of digital defense with Bennett Franklin’s 9-month Cyber Security & Ethical Hacking program, a comprehensive training experience designed to equip you with the technical skills and strategic mindset needed to tackle today’s sophisticated cyber threats.
In a world where data breaches, cyberattacks, and digital espionage are rising rapidly, cybersecurity professionals are in high demand. This program offers a robust, hands-on curriculum that dives deep into core areas such as network security, ethical hacking, penetration testing, cryptography, threat intelligence, malware analysis, firewalls, and vulnerability assessment.
Learn directly from experienced cybersecurity experts through live, interactive sessions, and apply your skills in real-world simulations and virtual labs that mirror the evolving threat landscape. You’ll gain a practical understanding of how to identify vulnerabilities, secure digital infrastructures, and respond to attacks using industry-standard tools and techniques.
Whether you’re a recent graduate with a passion for ethical hacking or a working IT professional aiming to pivot into cybersecurity, this program is tailored to suit your goals. The flexible online format allows you to study at your own pace without disrupting your professional commitments, while still engaging in a structured, career-focused learning environment.
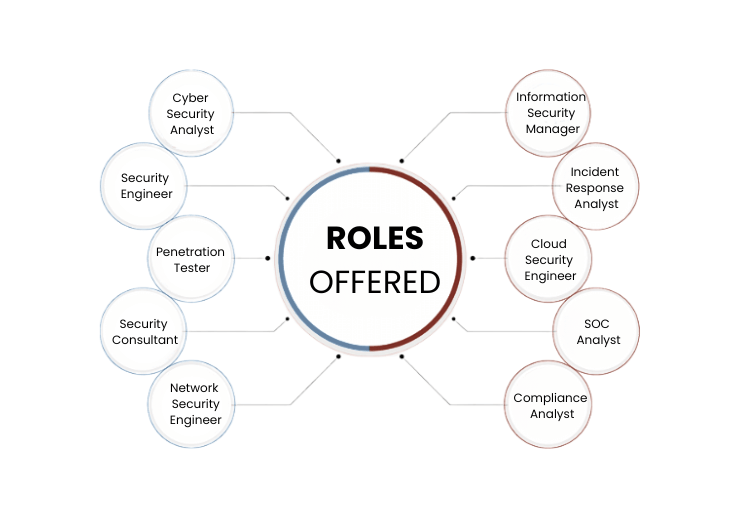
By the end of this immersive 9-month journey, you’ll be ready to take on job roles such as Cyber Security Analyst, Penetration Tester, Network Security Specialist, Ethical Hacker, and more. You’ll also be prepared for globally recognized certifications, enhancing your credibility and employability in a competitive job market.
Join Bennett Franklin’s Cyber Security & Ethical Hacking program today and take your first step toward a high-impact career securing the digital world—one skill, one system, and one solution at a time.
Industry growth projected till 2030 globally.
Unfilled roles in cyber security expected by 2025
Cyber security market to hit $248B by 2026.
Average salary of cyber security professionals.
See which benefits you can derive from joining this program.
An overview of what you will learn from this program.
| What is Cybersecurity? |
| The significance of Cybersecurity in the modern world |
| The evolving cyber threat landscape |
| The role of cybersecurity professionals |
| Understanding the fundamentals of computer networks |
| Different types of networks (LAN, WAN, MAN) |
| Exploring network topologies (Star, Bus, Ring) |
| The OSI (Open Systems Interconnection) model and its seven layers |
| A deep dive into the OSI Model layers |
| The TCP/IP Model and its relationship to OSI |
| Detailed exploration of IPv4 addressing and subnetting |
| Introduction to IPv6 and its advantages |
| Mastering IPv4 addressing, subnets, and CIDR notation |
| Practical subnetting exercises and examples |
| The importance of IPv6 and its adoption challenges |
| Hands-on IPv6 configuration and addressing |
| The origins and philosophy of Linux |
| What is Open-Source Software, and why is it important? |
| Overview of popular Linux distributions |
| Introduction to Linux Kernel and its role |
| Understanding the Linux Kernel architecture |
| Exploring different Linux Shells (e.g., Bash, Zsh) |
| Navigating the Linux file system using the command line |
| Practical exercises in accessing the command line |
| Navigating the Linux file system hierarchy |
| Detailed file and directory management commands |
| Creating, moving, copying, and deleting files and directories |
| Practical exercises in file management |
| Creating, viewing, and editing text files with Linux commands |
| Redirecting input and output streams |
| Working with text editors (e.g., Vi, Nano) |
| Hands-on text file editing and manipulation |
| Understanding user and group concepts in Linux |
| Gaining superuser privileges with sudo |
| Managing local user accounts: creation, modification, and deletion |
| Hands-on user and group management tasks |
| In-depth exploration of Linux file permissions |
| Interpreting permission settings (read, write, execute) |
| Managing file permissions from the command line |
| Practical exercises in permission management |
| Advanced file permission concepts (e.g., chmod, chown) |
| Default permissions and access control |
| Configuring secure file access |
| Real-world scenarios and troubleshooting |
| Comprehensive review of Linux fundamentals |
| Practical exercises and challenges |
| Troubleshooting common Linux issues |
| Preparing for further Linux exploration |
| Defining Ethical Hacking and its objectives |
| Elements of Security: Confidentiality, Integrity, Availability |
| The ethical hacker's code of conduct |
| Phases of Hacking: Reconnaissance, Scanning, Gaining Access, Maintaining Access, Covering Tracks |
| Categorizing hackers: White Hat, Black Hat, Gray Hat |
| Common types of cyberattacks: Malware, Phishing, DDoS, etc. |
| Scope and career opportunities in Ethical Hacking |
| Building ethical hacking skills and certifications |
| Understanding Footprinting in Ethical Hacking |
| The significance of Footprinting in the reconnaissance phase |
| Legal and ethical considerations in Footprinting |
| Footprinting techniques and tools |
| Leveraging search engines for Footprinting |
| Advanced Google Hacking techniques |
| Footprinting domains and subdomains |
| Practical exercises in Footprinting |
| Passive Footprinting methods and tools |
| Email Footprinting and its importance |
| DNS information gathering and Footprinting |
| Real-world passive Footprinting scenarios |
| Understanding Domain Name System (DNS) |
| Types of DNS records (A, MX, CNAME, etc.) |
| Leveraging DNS for Footprinting |
| Email Footprinting techniques and tools |
| Introduction to Network Scanning |
| Banner grabbing: Extracting information from network services |
| In-depth exploration of Nmap scanning tool |
| Practical Nmap scanning exercises |
| Advanced Nmap scanning options and strategies |
| Detecting and evading firewalls during scanning |
| Hands-on Nmap scanning scenarios |
| Best practices in network scanning |
| The significance of Enumeration in Ethical Hacking |
| Understanding ports and services enumeration |
| Enumerating common ports and services |
| Practical enumeration exercises |
| Techniques for service enumeration |
| Gathering information about running services |
| Hands-on service enumeration in real-world scenarios |
| Documenting findings for further analysis |
Explore real-world projects across diverse industries.
Detect threats across network traffic
Host-based monitoring for threat alerts
Trap and analyze hacker behaviors
Analyze memory dumps for malware
Control external hardware access
Test vulnerabilities in app protocols
Globally trusted leader in cybersecurity education.
Courses built with input from industry professionals.
Expert instructors with deep domain expertise.
Real labs, live tools, and enterprise case studies.
Career Support Services
Worked at companies like Google, Amazon, etc.
Over 200+ top global hiring partners.
Highest CTC reported $250,000 per year.
Average salary hike of 87% post-course.
How to Enroll Easily

Bennett Franklin’s PGP in Cyber Security is built for beginners and professionals alike. It combines tools, real-world cases, labs, and certification prep for job readiness.
All sessions are recorded and available on the learning portal. You’ll also get summaries and support notes.
You can work as an Ethical Hacker, Security Analyst, SOC Analyst, Penetration Tester, Forensics Expert, and more.
Yes, the course is fully online with live sessions, recordings, and 24/7 support.
Anyone interested in security and digital protection can apply. No coding or IT background is mandatory — we start from fundamentals.